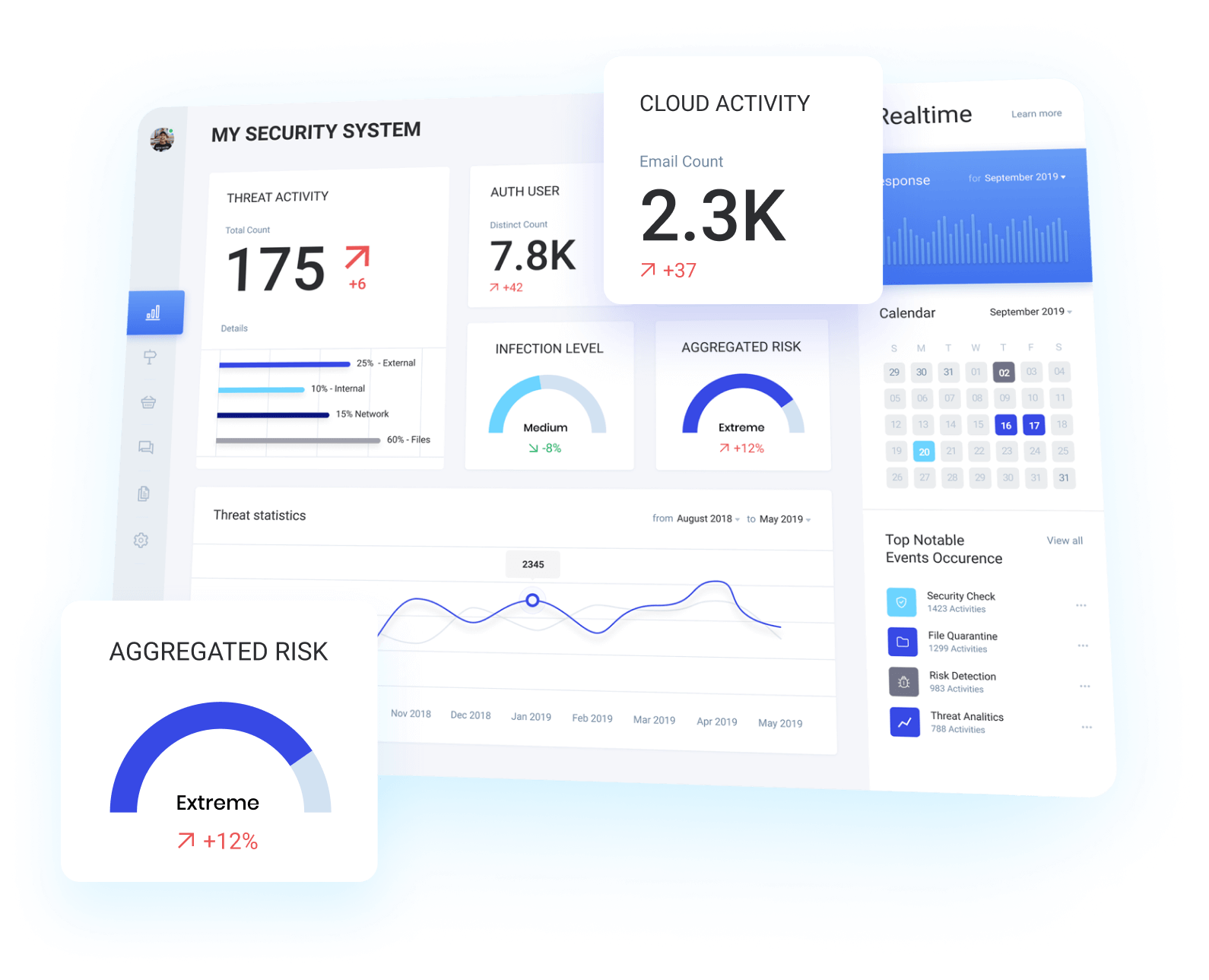
Defending your assets from possible threats

custom hardening guides for any product or service
We produce hardening guides for a wide range of products and services from Operating Systems, Application Services, Email Gateways, all the way through to Network Firewalls.


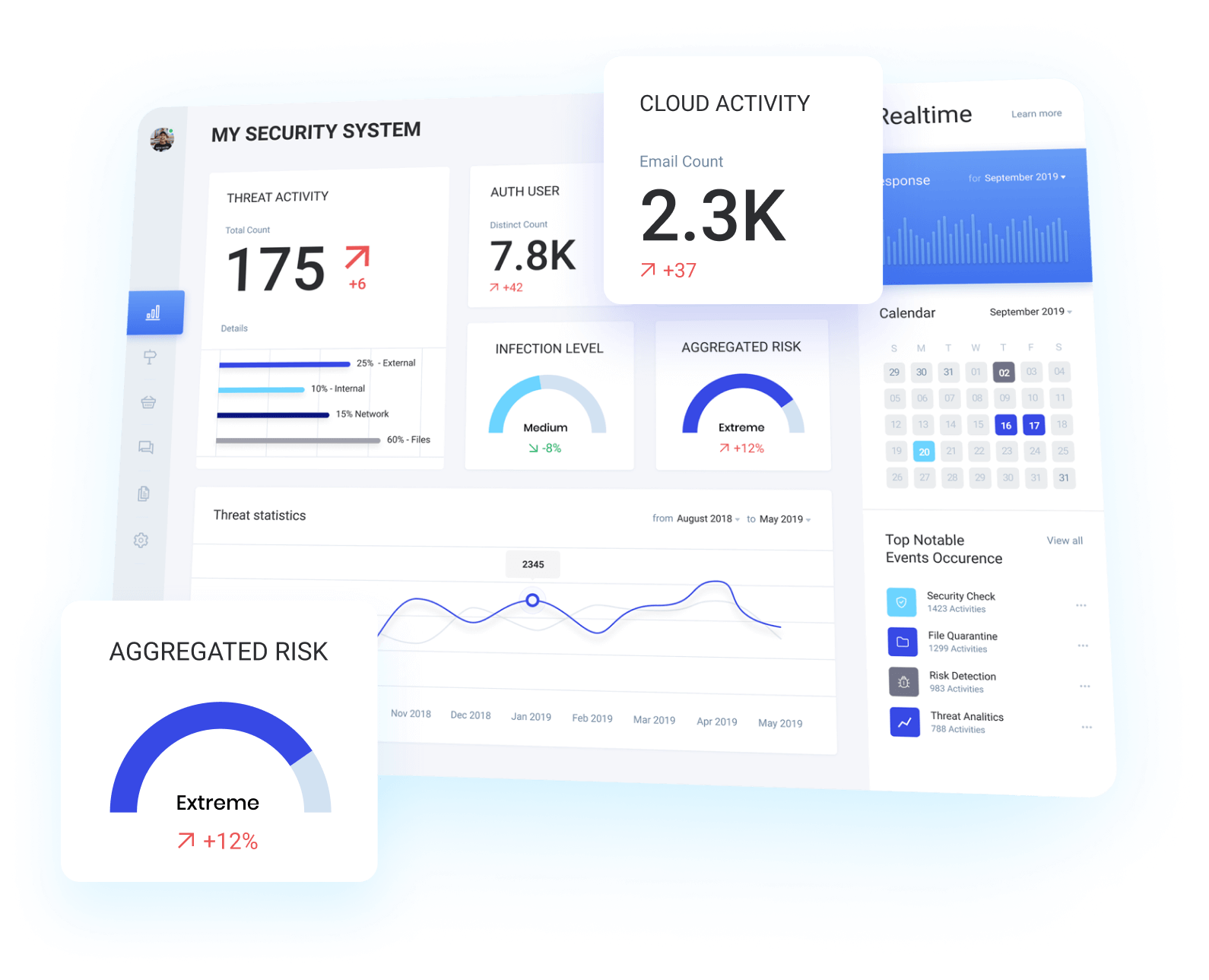
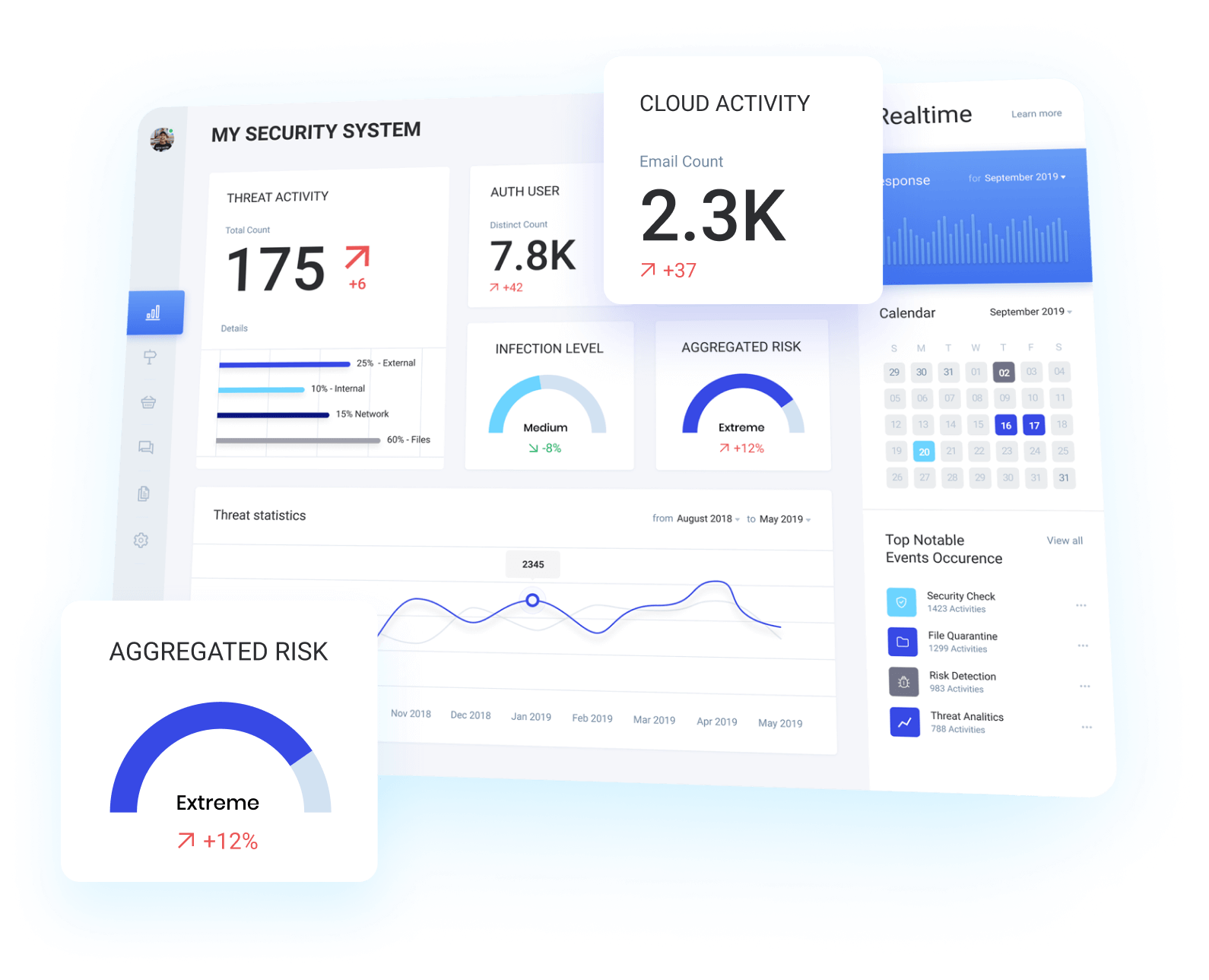
Internal Architecture & Service review
An organisations environment is only as secure as its weakest link, ensuring that the services and configurations within your architecture meet or exceed your security requirements can save you both time and money.
Architecture review
Our team will work with you to perform a review of your architecture, services, and configurations.
Security recommendations
We will provide recommendations on how you can improve the overall security posture of your implementation.
Service review report
We will document all findings & recommendations in a Security Architecture & Service Review report for your review.
case studies
LARGE ENVIRONMENTS FAIL TO MEET INDUSTRY STANDARDS
ALCHEMY'S DEFENSIVE AND MITIGATION STRATEGIES
Alchemy developed a process that allowed the business to align both their defensive and mitigation strategies against the MITRE ATT&CK framework.
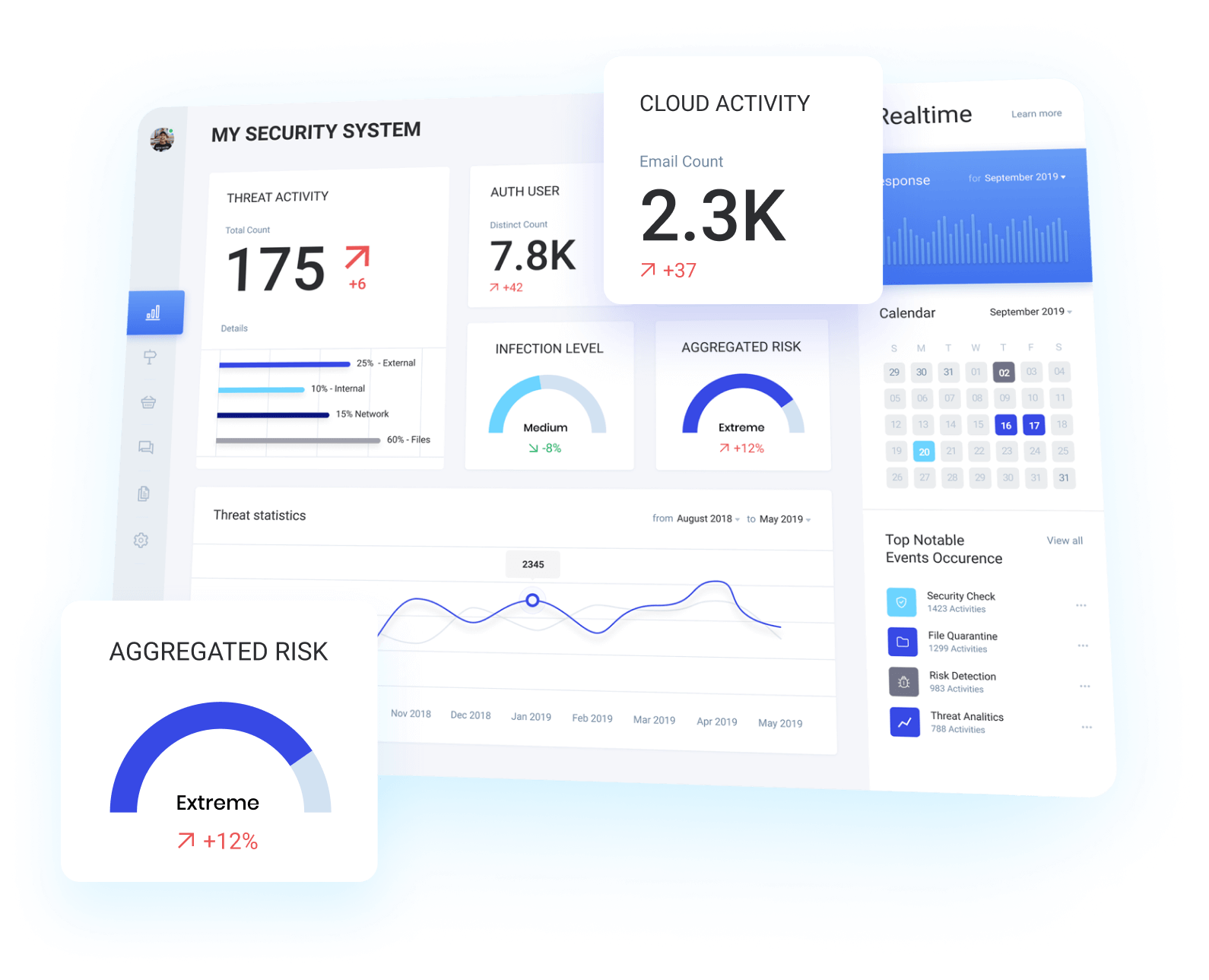
STRATEGICALLY ADDRESSING GAPS IN DEFENSIVE CAPABILITIES
This allowed the business to strategically address gaps in their defensive capabilities through configuration changes on existing products. The framework also allowed the business to strategically invest in product to fill identified gaps in defensive capabilities while avoiding product overlap to net a better return on investment.
SUCCESSFUL MONITORING AND MITIGATION OF TTPs
The MITRE ATT&CK framework was utilised to allow the business to align their technical mitigation and monitoring capabilities with real life tactics, techniques and procedures used by threat actors. This process allows organisations to identify gaps in these capabilities as well as processes or technologies that could be utilised to both monitor and mitigate a broad range of TTPs.
LARGE ENVIRONMENTS FAIL TO MEET INDUSTRY STANDARDS
It is quite common for large environments to have cyber security strategies in place. However generally these are aligned to a none technical or non-industry standard framework.
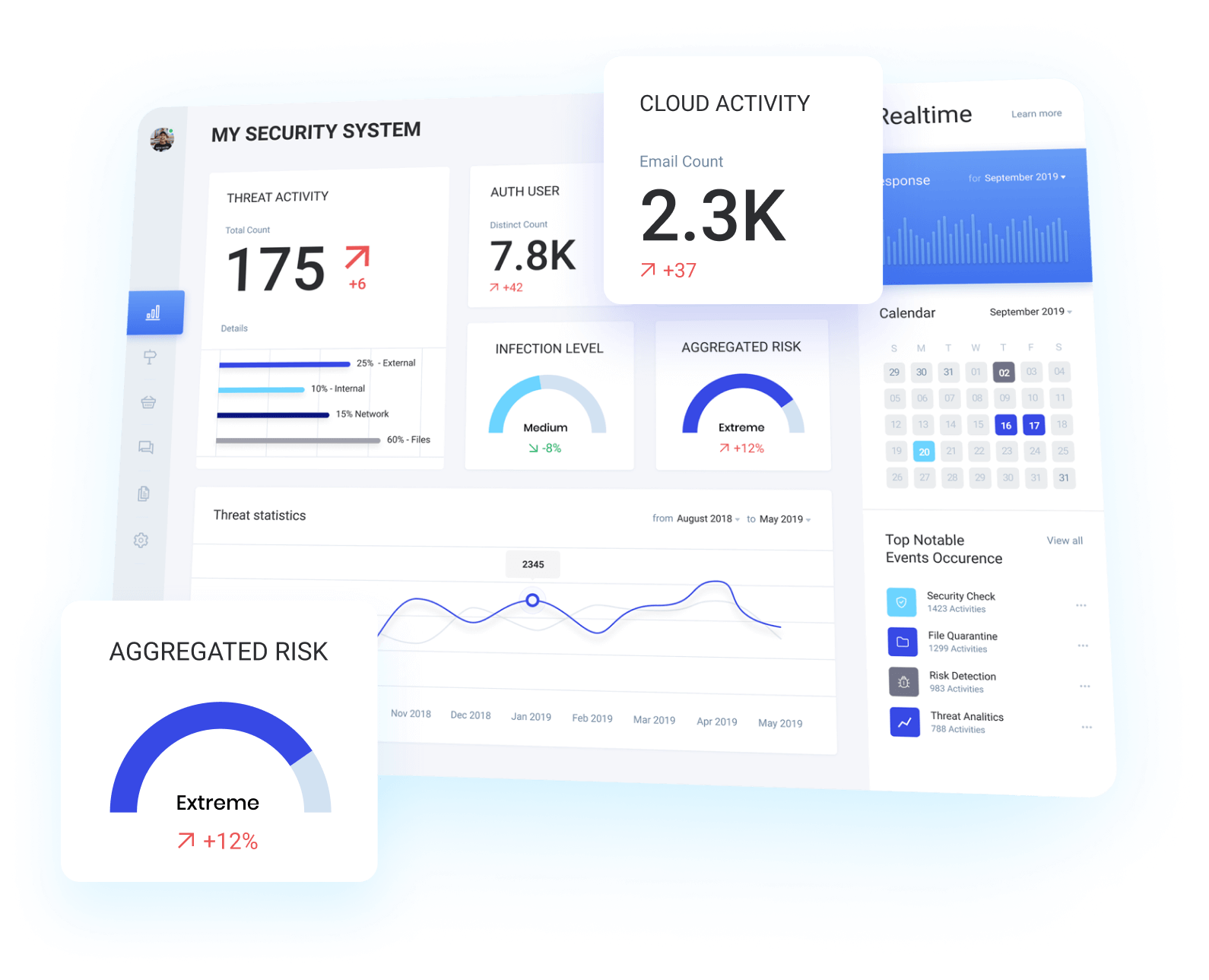
Our Unique Process We Developed Over 10 years.
Alchemy Security Consulting Pty Ltd provides a broad range of security assessment services to assist our customers in identifying vulnerabilities and maturing their defensive capabilities.
scoping
The scope will define the objectives, constraints, scheduling and reporting requirements for the assessment.
assessment execution
We will execute the assessment in line with the agreed scope.
reporting
All findings will be documented in a risk prioritised report detailing all findings and recommended actions.
remediation testing
A retest of key findings is performed to validate that remediation actions by the customer have successfully mitigated identified vulnerabilities without introducing further vulnerabilities or risks.
List all the benefits